Photo by Clay Banks on Unsplash
In the beginning, people created computers. A few years later, people decided to create malware. Firstly, we need to clarify what malware, virus, worms and trojans are. Malware is a catch-all phrase for all malicious software regardless of how it operates; viruses, worms and trojans fall under the malware term. Viruses spread through computers, firstly through physical input devices and now through the Internet. Usually existing within executable files, they can be on your computer without causing any negative effects until they are run. A worm is a type of virus that can spread without help from a person, for example travelling through an open port in your computer to other computers on your network. Finally, a trojan is a program that allows the creator access to your computer by pretending to be a genuine application (think about the trojan horse).
The first ever computer malware was a virus. A virus is a specific type of malware that is designed to copy itself and spread everywhere [1]. It was created in 1982 and was called Elk Cloner and spread by attaching itself to a game. When the floppy disk was inserted, it wrote the virus to the computer’s memory. When an uninfected floppy disk was inserted the virus would be copied to that floppy disk. Luckily the virus was harmless and only displayed a poem when the game was launched for the 50th time.
Unfortunately, since 1982 there have been many different threats and malware that are not harmless and do more damage than displaying a poem. Some destructive malware have been known to evolve, such as becoming more advanced, being encapsulated in a different type of malware, or even being completely rewritten with different attack vectors.
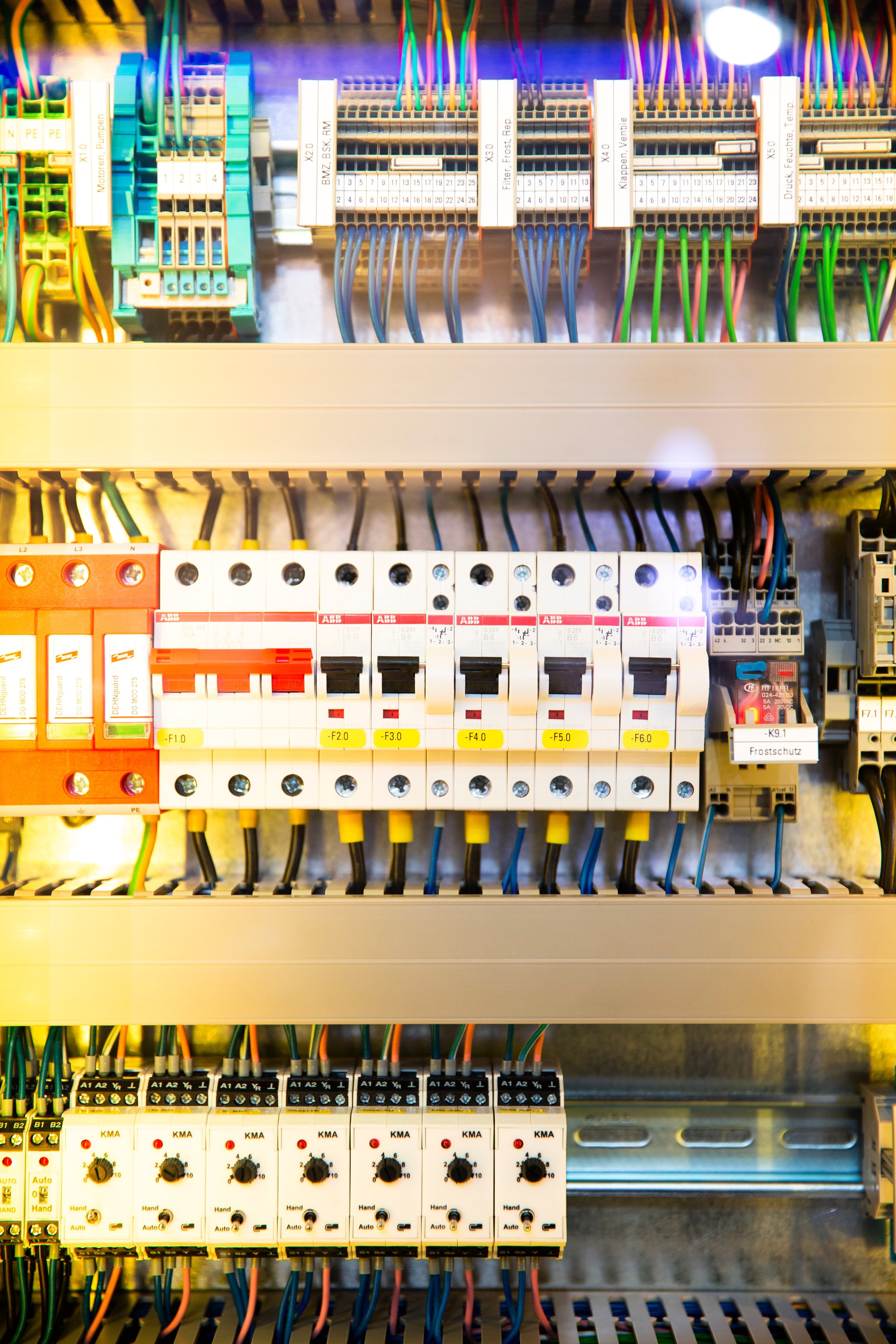
Stuxnet specfically targeted SCADA equipment as seen above, specifically in the Iranium Nuclear facilities - Photo by Markus Spiske on Unsplash
Stuxnet - Is a worm that targets SCADA systems and PLCs using four Windows zero-day exploits. Siemens then developed a removal tool and advised an audit of PLCs and updating password access codes. About 6 years later, in 2019, research from the Alphabet’s security company, Chronicle has revealed that the Stuxnet found previously may have only been a module for a larger platform. Having been tied with other cyber espionage families like Flame, Duqu and the Equation Group, Chronicle has concluded that Stuxnet was the result of a collaborative framework with a bunch of different groups. In addition, the researchers also found some Flowershop code that was used in the Stuxnet module which may indicate collaboration between the two groups. This finding shows that although we may have protected our network against a specific malware, there are many different types of the same malware strain that attacks different aspects of our network.
WannaCry - is a ransomware attack that targeted Microsoft Windows devices. It was delivered via EternalBlue, an exploit developed by the NSA for Windows systems. Although Microsoft had released a patch to close the exploit, millions of devices running older Windows versions were affected. Furthermore, a kill switch was discovered and activated by an expert called MalwareTech. Since the exploit was patched and kill switch activated, there hasn’t been any news about WannaCry. However, other malware like Emotet has taken over the attention of the cyber world. Research has shown that Emotet is spread via a trojan, TrickBot, using the same EternalBlue vulnerability that WannaCry used.
Petya was initially spread via Email, but soon progressed to more covert means of travel - Photo by Justin Morgan on Unsplash
Petya/NotPetya - A family of malware that was discovered in 2016. The first variant spread via infected email attachments which when opened releases the malware on the victim’s computer. Petya, while devastating to an individual device, did not manage to cause widespread damage and only affected a few devices. It tried to socially engineer users to open a fake PDF file and give it admin permissions. Petya only prevented users from booting into Windows, the files and data remained unencrypted and safe. NotPetya, discovered in 2017 spread through the EternalBlue vulnerability and encrypted/destroyed storage devices preventing recovery of data. In addition, NotPetya targeted critical national infrastructure instead of any computer that received an infected email attachment. This family of malware is a good example of how although the malware may have some similarities (in this case, being a virus, attacking the Master File Table and asking for a ransom), they can vary in a few critical ways [2].
The evolution of malware will not stop. Although it has been a few years since we have heard about some malware families, we have to assume that they are still being developed. Some malware evolve to encompass a larger skill set and spread via more than one method while others evolve to take advantage of existing vulnerabilities in order to infect more devices. It’s important that we keep Critical National Infrastructure safe, secure, and updated.
If you are worried about any of the previously mentioned vulnerabilities, or are concerned about cyber attacks in general; contact us today for a no obligation chat on how we at Awen Collective can help you today!